Quan chức an ninh Ukraine cho biết những người bảo vệ mặt trận mạng luôn căng thẳng khi họ phải đối đầu các cuộc tấn công gần như mỗi ngày.
Trong những ngày đầu tiên sau khi Nga phát động chiến dịch tại Ukraine, Illia Vitiuk và các đồng nghiệp đã lo sợ điều tồi tệ nhất: Kiev sụp đổ.
Vitiuk, người đứng đầu bộ phận mạng của Cơ quan An ninh Ukraine (SBU), lực lượng phản gián hàng đầu đất nước, nói rằng đã chiến đấu với tin tặc và gián điệp Nga suốt nhiều năm. Nhưng vào ngày 24/2/2022, SBU được giao nhiệm vụ khác. Họ phải vận chuyển các máy chủ và cơ sở hạ tầng kỹ thuật quan trọng ra khỏi Kiev để bảo vệ chúng trước những cuộc tấn công từ Nga.
"Tên lửa bắn trúng Kiev và mọi người vội vã sơ tán khỏi thành phố. Chúng tôi đã cố gắng liên hệ với một số cơ quan và người quản lý cơ sở hạ tầng quan trọng nhưng đôi khi nhận được những câu trả lời như 'quản trị viên hệ thống đã đi vắng vì gia đình anh ấy đang ở Bucha và anh ấy cần đưa họ rời khỏi Bucha", Vitiuk nhớ lại.
"Kiev khi đó có nguy cơ bị bao vây", ông nói tiếp. "Vì vậy, chúng tôi cần chuyển những cơ sở dữ liệu và phần cứng quan trọng nhất ra khỏi Kiev".
Cuối cùng, nhờ Vitiuk và các chuyên gia "chiến tranh mạng" của ông, tin tặc Nga đã không thể phá hủy cơ sở hạ tầng kỹ thuật số Ukraine trong những ngày đầu xung đột.
Tuy nhiên, Ukraine phải hứng chịu hàng loạt các cuộc tấn công mạng, lên đến gần 3.000 vụ trong năm nay, theo Vitiuk.
Cùng với các cuộc tấn công bằng tên lửa và máy bay không người lái (UAV), các hoạt động tấn công mạng do tin tặc Nga tiến hành đã làm suy yếu đáng kể cơ sở hạ tầng Ukraine, đặc biệt là mạng lưới điện. Tin tặc Nga cũng thu được thông tin nhạy cảm để hỗ trợ cho chiến dịch của Moskva.

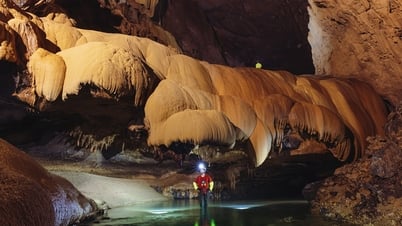
Illia Vitiuk, lãnh đạo bộ phận mạng của Cơ quan An ninh Ukraine. Ảnh: SBU
Bắt đầu từ khoảng tháng 12/2021, các cuộc tấn công mạng từ Nga đã gia tăng mạnh mẽ khiến nhiều người trong khu vực tư nhân lo sợ kịch bản tồi tệ nhất sắp xảy ra.
Cùng khoảng thời gian đó, các đại diện từ Bộ Tư lệnh Không gian mạng Mỹ đã tới Kiev giúp kiểm tra các thành phần quan trọng trong cơ sở hạ tầng mạng Ukraine mà họ cho rằng sẽ là "tâm điểm của các cuộc tấn công", Vitiuk cho biết.
"Và nó đã xảy ra đúng như thế", ông nói, thêm rằng phía Mỹ còn cung cấp cả những phần cứng và phần mềm mà chính phủ Ukraine vẫn sử dụng cho đến hiện tại để bảo vệ hạ tầng mạng của mình.
Nga sau đó triển khai một số công cụ tấn công mạng nhằm vào khoảng 70 cơ sở nhà nước Ukraine và đánh sập hàng chục trang web chính phủ. Họ tuyên bố xâm nhập vào Diia, ứng dụng kỹ thuật số được người Ukraine sử dụng để lưu trữ tài liệu, cũng như can thiệp vào hàng loạt dịch vụ trực tuyến khác. Vào tháng 2/2022, tin tặc Nga tấn công dịch vụ tài chính để khiến người dân Ukraine nghĩ rằng họ không thể tiếp cận được tiền của mình trong trường hợp khẩn cấp.
Vitiuk cho hay có vẻ như tin tặc Nga lúc bấy giờ đang "thử nghiệm và chuẩn bị cho điều gì lớn lao".
Mọi thứ trở nên căng thẳng hơn bao giờ hết vào đêm 23/2/2022, ngay trước khi xung đột nổ ra. "Chúng tôi bắt đầu gặp hàng loạt cuộc tấn công mạng", Vitiuk kể. "Chúng tôi phải chống chọi lại chiến dịch tâm lý mà họ phát động".
Một số cuộc tấn công đã đánh sập ViaSat, hệ thống liên lạc vệ tinh mà quân đội Ukraine sử dụng vào thời điểm đó. Khi không thể ngăn cản lực lượng vũ trang Ukraine liên lạc với nhau, Vitiuk cho biết Nga dường như đã triệu tập mọi lực lượng không gian mạng họ có để tấn công, nhắm vào các phương tiện thông tin đại chúng, nhà cung cấp dịch vụ truyền thông, trang web của chính quyền địa phương và các bộ.
"Ngay từ đầu, chúng tôi nhận thấy rõ rằng họ đã cố gắng sử dụng tất cả những con át chủ bài trong tay", ông nói.
Với Ukraine, thách thức chính trong giai đoạn đó là việc phối hợp với chuyên gia an ninh mạng tại các cơ quan chính phủ và tổ chức quan trọng khác, nhiều người trong số họ đang bị đe dọa tính mạng trước đạn pháo. Đây là lúc SBU bắt đầu chuyển các máy chủ khỏi Kiev.
Khi được hỏi liệu những cuộc tấn công ban đầu có tác động lâu dài hay không, Vitiuk nói rằng chỉ một số hệ thống bị hư hỏng và một lượng dữ liệu nhỏ bị đánh cắp.
"Không có hệ thống chủ chốt nào bị hư hại", ông cho biết. "Chúng tôi làm việc 24/7. Chúng tôi đã giải quyết vấn đề khá nhanh".

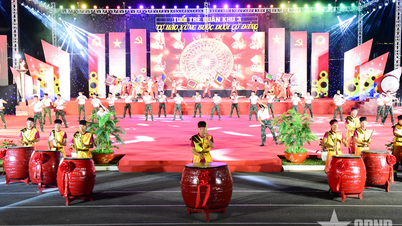
Binh sĩ Ukraine nghiên cứu dữ liệu trên máy tính bảng trước khi khai hỏa ở Bakhmut hồi tháng một. Ảnh: Reuters
Sau thất bại của chiến dịch đánh nhanh thắng nhanh, Vitiuk cho biết SBU đã quan sát thấy tin tặc Nga chuyển đổi chiến thuật, chủ yếu hướng tới thu thập thông tin tình báo và làm gián đoạn lưới điện.
"Kể từ mùa hè, họ đã hiểu rằng cuộc xung đột này sẽ kéo dài hơn và họ cần chuyển sang một điều gì đó nghiêm túc hơn", ông nói.
Theo Vitiuk, Nga cũng cố gắng xâm nhập vào các hệ thống lập kế hoạch hoạt động quân sự của Ukraine, trong đó có nền tảng Delta. SBU gần đây công bố một báo cáo chi tiết về việc các sĩ quan tình báo quân đội Nga ở tiền tuyến cố lấy máy tính bảng Android mà sĩ quan Ukraine sử dụng, nhằm đột nhập vào Delta để thu thập thông tin tình báo cũng như việc quân đội Ukraine dùng thiết bị liên lạc di động Starlink từ công ty SpaceX của tỷ phú Elon Musk.
Bằng cách này, Nga có thể xác định vị trí của một số thiết bị liên kết với Starlink và nhắm mục tiêu tốt hơn cho các cuộc tấn công tên lửa.
SBU tuyên bố họ đã thành công ngăn chặn Nga tiếp cận Delta và các chương trình tương tự nhưng Vitiuk thừa nhận họ vẫn để mất một số thông tin.

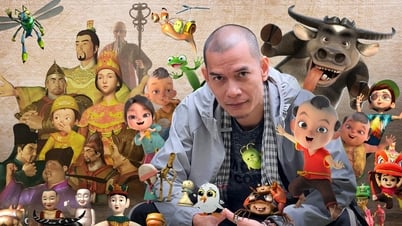
Lính Ukraine cùng thiết bị Starlink tại Kreminna hồi tháng 2. Ảnh: Reuters
Khi xung đột nổ ra, gần như tất cả mọi người dân Ukraine đều tham gia tình nguyện, quyên góp tiền hoặc làm việc trực tiếp với chính phủ để hỗ trợ nỗ lực chiến đấu. Trong số đó có cộng đồng công nghệ thông tin (IT).
Nhiều người đang làm cố vấn bán thời gian cho các cơ quan chính phủ trong khi những người khác tham gia với vai trò quyết liệt hơn. Nổi bật nhất là Đội quân IT, được Bộ Chuyển đổi Kỹ thuật số Ukraine hỗ trợ ngay từ đầu cuộc xung đột. Nhóm chủ yếu tập trung vào phát triển phần mềm và công cụ cho người dân để thực hiện tấn công từ chối dịch vụ (DoS) nhằm vào các mục tiêu Nga, phát triển các phần mềm tự động giúp chính phủ thu thập thông tin tình báo.
Tham gia vào nỗ lực này có các nhóm như Liên minh Mạng Ukraine, Hackyourmom, dự án do doanh nhân an ninh mạng người Ukraine Nykyta Kynsh khởi xướng, và Inform Napalm, trang web chuyên điều tra dữ liệu bị rò rỉ và xác định các hacker Nga.
Nhiều nhóm tuyên bố các hoạt động của họ một cách công khai nhưng một số nhóm khác hoạt động bí mật hơn.
Dù vậy, giới chuyên gia an ninh mạng cảnh báo những cuộc tấn công do các tình nguyện viên thực hiện, đôi khi xuất hiện ngẫu nhiên và thường không đạt được hiệu quả lâu dài, có thể gây hại nhiều hơn là mang lại lợi ích cho những hoạt động bí mật.
Bất chấp những lo ngại, Vitiuk lập luận rằng mọi kỹ năng của các tình nguyên viên đều có giá trị ở một mức độ nhất định. "Điều này giống như bảo vệ lãnh thổ trên mạng của chúng tôi", ông nói. "Nhiệm vụ của chúng tôi là theo dõi và tìm hiểu rõ về những tình nguyện viên, chỉ đạo họ hoặc cho họ lời khuyên về cách thức làm việc hiệu quả hơn".
Khi được hỏi về mối đe dọa trên không gian mạng từ Nga trong tương lai, Vitiuk dự đoán các cuộc tấn công sẽ tiếp tục với cường độ như năm trước, đặc biệt là khi bước vào mùa đông.
Các cuộc tấn công có thể trở nên phức tạp hơn, nhưng việc tăng cường độ sẽ là thách thức với Nga vì số lượng chuyên gia lành nghệ hiện tại của họ còn hạn chế. "Họ cần nhiều người hơn", Vitiuk nói.
Vitiuk cho biết SBU đang tập trung chuẩn bị cho mùa đông, hợp tác với Bộ Năng lượng và các chuyên gia khác để bảo vệ lưới điện dựa trên bài học kinh nghiệm năm ngoái.
Ông thừa nhận bất chấp tất cả những thành công, họ vẫn cần được giúp đỡ để tiếp tục củng cố cơ sở hạ tầng quan trọng. Nhu cầu này đặc biệt cấp thiết ở cấp địa phương, nơi có ít nguồn lực hơn.
Trong một hội nghị gần đây ở Estonia, Vitiuk kêu gọi các công ty an ninh mạng đến Ukraine giúp đánh giá nhu cầu của nước này, từ cơ sở hạ tầng kỹ thuật đến phần cứng, phần mềm và trực tiếp gửi thiết bị thay vì chuyển tiền.
Ông bày tỏ lo ngại về vấn đề tham nhũng trong nước. "Chúng tôi không cần tiền. Chúng tôi cần một hệ thống minh bạch nhất có thể", ông nhấn mạnh.
Vitiuk cho rằng ngay cả khi xung đột kết thúc, an ninh mạng vẫn sẽ là vấn đề được chú trọng đặc biệt. "Các học thuyết mới sẽ được viết và áp dụng theo những gì đã xảy ra ở Ukraine, theo kinh nghiệm của chúng tôi", ông nói.
Vũ Hoàng (Theo NPR)
Source link



































































































Bình luận (0)